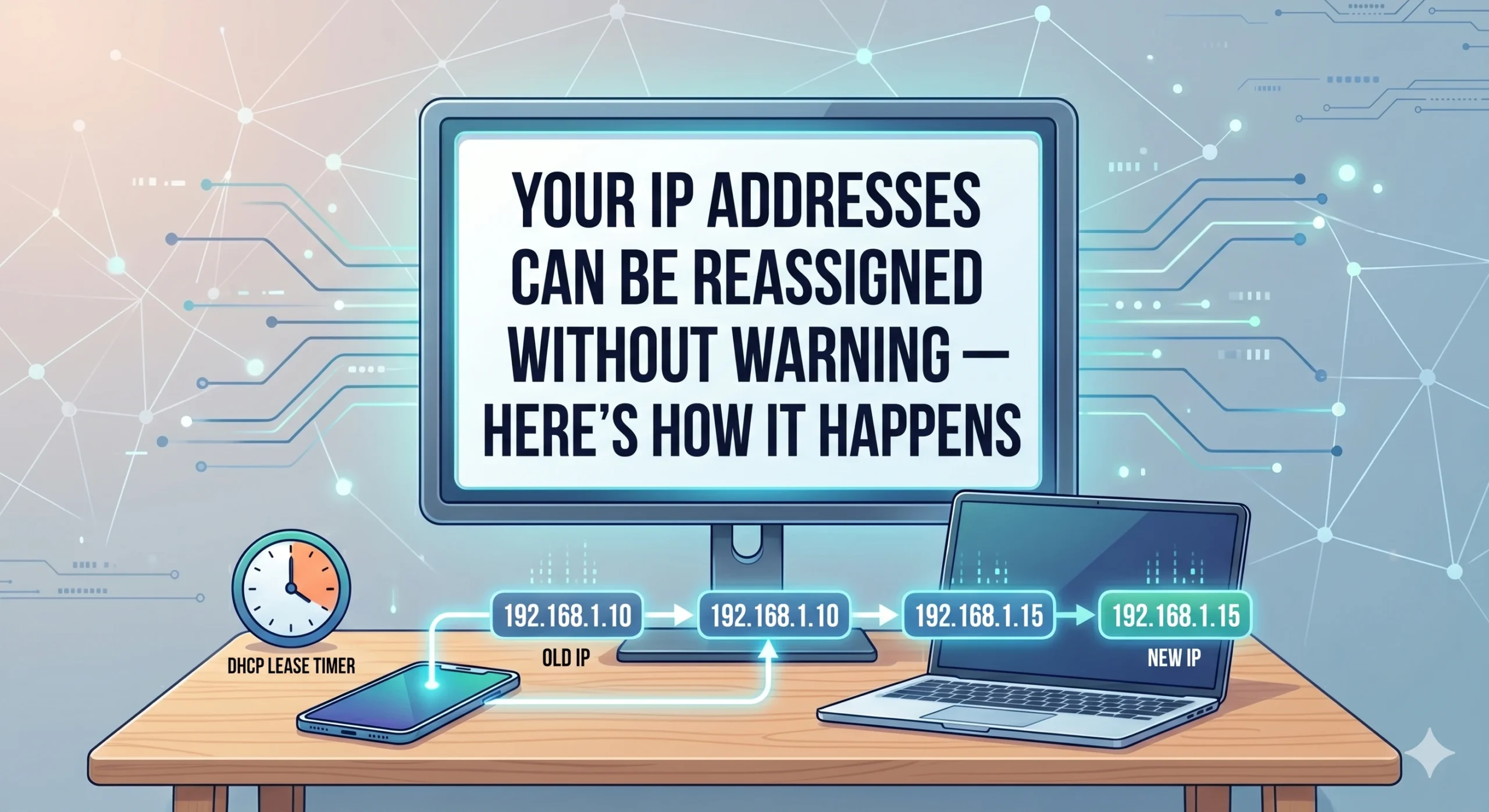
Your IP addresses can be reassigned without warning — here’s how it happens
Table of Contents
Toggle
Standfirst:
IPv4 scarcity, transfer markets, and registry-layer dependency are quietly reshaping internet infrastructure — often without businesses realising the risk.
Many organisations assume long-used IP addresses are permanent assets, even when continuity depends on external providers and registry structures.
Reassignment increasingly happens through routine lifecycle events including provider changes, transfers, bankruptcies, cloud recycling, and governance shifts.
Most companies assume their IP addresses are permanent
For years, businesses treated IP addresses as stable infrastructure.
Once an organisation deployed an address range across production systems — customer allowlists, VPNs, firewalls, APIs, SaaS platforms, DNS records, and email servers — those addresses became embedded into daily operations.
Over time, the addresses effectively became part of the organisation’s identity.
That assumption made sense during the early internet era, when IPv4 allocations were abundant and address transfers were uncommon.
But the modern internet operates very differently.
Today, IPv4 addresses move continuously through a global ecosystem shaped by scarcity, leasing, transfers, provider dependency, and secondary market activity. What once behaved like static infrastructure increasingly behaves like managed operational inventory.
The result is a growing continuity problem that many enterprises still fail to recognise until disruption begins.
The misunderstanding starts with “ownership”
Most organisations believe that if they have used an IP range for years, they effectively own it.
Operationally, that can appear true.
Administratively, however, the situation is often more complicated.
Many enterprises operate using address space tied to:
internet service providers
datacentre operators
cloud platforms
leasing arrangements
upstream registry members
The business may control day-to-day usage while the deeper continuity structure remains dependent on external entities.
For years, this distinction rarely mattered. Allocations remained relatively stable, providers changed slowly, and IPv4 exhaustion had not yet transformed address space into a high-value operational asset.
That environment no longer exists.
Across today’s IPv4 market, operational usage and long-term continuity are increasingly separate things.
Here’s how reassignment actually happens
In most cases, IP reassignment does not happen through a dramatic technical failure.
It unfolds gradually through ordinary operational events that accumulate underneath production infrastructure.
A typical lifecycle often looks like this.
Stage 1: The addresses become deeply embedded
A company deploys an IPv4 range into production.
Over time, the addresses become trusted across multiple external systems:
customers allowlist them
suppliers build firewall rules around them
remote offices configure VPN tunnels
SaaS platforms whitelist them
email reputation accumulates
security tools recognise them as trusted infrastructure
After years of uninterrupted use, everyone assumes the addresses are effectively permanent.
At this stage, very few organisations still think about who actually controls the registry relationship underneath the infrastructure.
Stage 2: The underlying stewardship sits elsewhere
In many enterprise environments, the company itself is not the direct registry holder.
Instead:
the ISP maintains allocation authority
the cloud provider controls reassignment
the upstream network operator manages routing relationships
a leasing intermediary maintains stewardship records
Operationally, nothing appears unstable.
But continuity increasingly depends on governance layers the enterprise does not directly control.
That separation often remains invisible until a business event forces change.
Stage 3: A routine lifecycle event triggers instability
This is where reassignment risk accelerates.
The trigger is often mundane:
a provider migration
a merger
a bankruptcy proceeding
a datacentre closure
contract termination
a transfer transaction
infrastructure consolidation
unused cloud resources being recycled
None of these events necessarily involve malicious activity.
In many cases, the reassignment process is entirely legitimate from a registry or provider perspective.
The problem is that downstream operational dependencies frequently outlive the administrative assumptions behind them.
Stage 4: Registry and routing control changes
Once stewardship changes, address continuity can shift surprisingly quickly.
Returned IPv4 resources may enter redistribution processes. Leased ranges may revert to upstream holders. Transfer transactions may move operational authority between unrelated organisations in entirely different jurisdictions.
This is one of the biggest structural changes in the modern internet economy.
IPv4 addresses are no longer behaving purely as technical identifiers. They increasingly function as transferable infrastructure assets moving through commercial markets.
That changes the continuity equation significantly.
A company may have routed an address range for years while still depending on contracts, providers, registry records, or lifecycle agreements that can change independently of the production network itself.
Stage 5: The operational fallout begins
This is where reassignment stops being an administrative issue and becomes a business continuity problem.
The newly reassigned address range may inherit years of historical baggage.
Email reputation problems
If the range previously hosted spam infrastructure or abusive services, email systems may immediately distrust legitimate traffic originating from the new operator.
Residual trust relationships
Old allowlists and firewall rules elsewhere on the internet may still trust the IP range long after stewardship changes.
SaaS authentication failures
Applications relying on IP-based authentication may suddenly reject legitimate traffic after renumbering or reassignment.
Threat intelligence confusion
Security databases often retain historical associations tied to IP reputation, creating attribution problems for new operators.
None of these failures require a cyberattack.
They emerge naturally from continuity assumptions surviving longer than the infrastructure relationships underneath them.
Real-world examples show the shift is already happening
The transformation of IPv4 into a transferable infrastructure asset is no longer theoretical.
One of the most widely discussed examples came during Nortel Networks’ bankruptcy proceedings, when its IPv4 portfolio was later acquired by Microsoft in a deal reportedly worth $7.5 million.
The transaction became a turning point for the industry because it demonstrated that IP addresses themselves had become financially valuable operational assets independent of physical infrastructure.
The implications extended far beyond one sale.
It signalled that address continuity could increasingly be shaped by:
insolvency proceedings
asset liquidation
transfer markets
investment activity
commercial restructuring
At the same time, cloud environments introduced another form of reassignment risk.
Public cloud providers routinely recycle unused public IP addresses between customers. Security researchers have repeatedly documented cases where recycled cloud infrastructure retained residual trust relationships because external organisations failed to remove outdated allowlists or authentication rules.
In several documented cloud security studies, reassigned infrastructure unexpectedly regained access to third-party systems purely because historical trust assumptions remained active.
The reassignment itself was legitimate.
The downstream assumptions were outdated.
Why the problem is becoming more serious
The reassignment issue is intensifying because IPv4 scarcity has fundamentally changed the market surrounding internet infrastructure.
Address space is now routinely:
leased
brokered
transferred
consolidated
liquidated
financially valued
Historically, many allocations remained relatively static inside universities, telecom operators, or long-established network operators.
Today, address space moves far more dynamically across commercial ecosystems.
That creates a very different operational environment from the one many enterprise systems were originally designed around.
The deeper issue is not simply scarcity.
It is that continuity increasingly depends on administrative resilience, stewardship quality, and lifecycle governance rather than purely technical uptime.
IPv6 reduces scarcity — but not continuity dependency
IPv6 may eventually reduce the economic pressure driving IPv4 transfers and reassignment activity.
But governance dependency itself does not disappear.
Organisations will still rely on:
providers
routing systems
registry frameworks
operational stewardship
lifecycle management
The internet’s addressing layer is no longer just technical infrastructure.
It is governed infrastructure.
And that means continuity increasingly depends on administrative structures that most businesses rarely monitor until something breaks.
The future of IP addresses is becoming fluid
The internet once assumed IP allocations were relatively stable and long-lived.
That era is fading.
Today, IP addresses behave more like movable infrastructure assets circulating through a constrained global system shaped by scarcity, governance, and operational dependency.
For enterprises, the most important lesson is not simply that reassignment can happen.
It is that reassignment often begins long before anyone notices operational symptoms.
An address range may appear stable for years while the stewardship, contractual control, routing authority, or registry dependency underneath it gradually changes hands.
By the time disruption surfaces inside production systems, the continuity assumptions may already have been broken for quite some time.
It refers to unused, underutilised, or poorly managed IPv4 address space within an organisation’s network infrastructure.
Because legacy network designs, fragmented governance, and lack of real-time visibility make optimisation difficult.
Yes. Most real-world systems still rely heavily on IPv4, making efficient management essential.
Increasingly yes, especially where IPv4 space is leased, traded, or requires additional acquisition.
Not technology — governance. Specifically, lack of centralised control and lifecycle